Displaying 49 - 51 of 51
04 Nov 2026 - 07 Nov 2026
Online instructor led
This course focuses on enhancing the protection and cyber resilience of Critical Information Infrastructures (CII). These include essential assets,…
Registration:
Open until 19 Oct 2026
Languages:
- English
24 Nov 2026 - 26 Nov 2026
Online instructor led
The course, “Ubiquitous Connectivity: Integration of Non-Terrestrial Networks (NTN) with Terrestrial Networks” is structured to provide participants…
Registration:
Open until 20 Oct 2026
Languages:
- English
30 Nov 2026 - 07 Dec 2026
Online instructor led
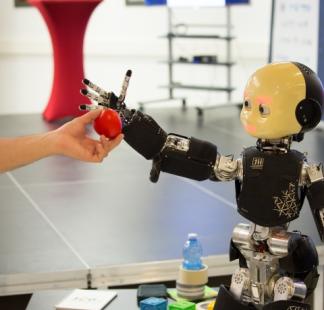
This course focuses on technical, business and regulatory aspects of Artificial Intelligence (AI) and Metaverse for future Internet and telecoms. It…
Registration:
Open until 29 Nov 2026
Languages:
- English